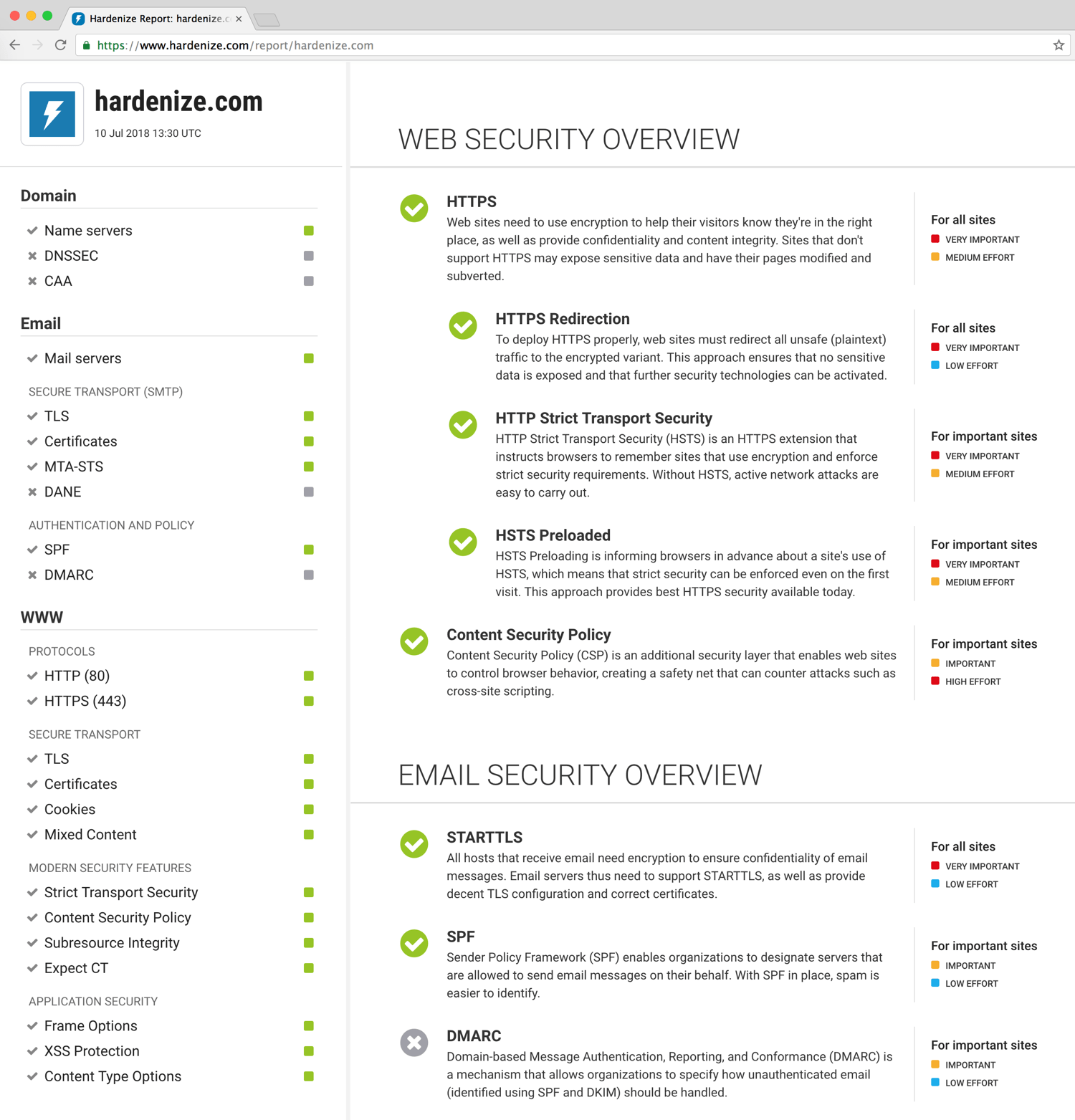
With so many security features to deploy and network services to configure, everybody needs help to understand what their networks look like. Our continuous monitoring and discovery services keep an eye on your infrastructure, monitor your certificates, prevent breakage, and enable you to have exactly the security you want.
Try our public report against your domain name: